IoT Development Services: The Complete Guide to Building Connected Products That Scale
Everything your team needs to evaluate, structure, and deliver a production-ready IoT system — from firmware to cloud.
- Professional IoT development services span the full lifecycle — hardware, firmware, connectivity, cloud, and applications — not just code delivery.
- A layered architecture (device, connectivity, cloud, application) must be designed as a coherent whole to avoid costly integration debt later.
- Custom development protects your IP and roadmap when pre-packaged platforms cannot meet your hardware, security, or integration requirements.
- Device management and secure OTA updates are non-negotiable operational foundations for any fleet operating at scale.
- Security must be designed in from day one — across device identity, encryption, firmware signing, and supply-chain controls.
- A unified, full-stack IoT engineering team reduces integration bugs, accelerates delivery, and provides a single point of accountability.
Table of Contents
- What do IoT development services actually involve?
- What is the typical architecture of an IoT solution?
- IoT solutions vs. IoT development services: What is the difference?
- When should you choose custom development over a ready-made platform?
- How do you select the right communication technology?
- Why is Device Management critical for connected devices?
- How can you implement secure OTA updates?
- How to secure an end-to-end IoT system?
- Handling scaling: Moving from 10 to 10,000+ devices
- Comparison: business need vs. how a boutique tech partner helps
- Transforming IoT data into actionable business insights
- What is the recommended workflow for a professional IoT project?
- How long does an IoT development project take?
- What factors influence the cost of IoT development services?
- Essential deliverables to request from your engineering partner
- Common mistakes in IoT projects and how to prevent them
- Why hire a full-stack IoT development team?
- Are IoT development services right for your business?
- Frequently asked questions
In today’s hyper-connected market, launching a successful connected product is no longer just about building a smart device — it’s about orchestrating a complex ecosystem of hardware, firmware, cloud infrastructure, and user-facing applications. Many scaleups and enterprises struggle to bridge the gap between a promising prototype and a production-ready system that can scale to thousands of devices without breaking. This is where professional IoT development services become a critical lever for growth, transforming technical complexity into a predictable, scalable business asset.
In this guide, your team will find a clear breakdown of what these services include, how to structure your project, and what to demand from your engineering partner to ensure long-term success. At Sentice, we work as a boutique tech partner that embeds senior engineers directly into your product organization — covering embedded systems, cloud infrastructure, and application layers as one end-to-end team.
What do IoT development services actually involve?
IoT development services encompass the full lifecycle of a connected product: hardware and firmware design, connectivity strategy, backend cloud infrastructure, data pipelines, and end-user applications. A professional service does not stop at code delivery — it covers architecture strategy, proof-of-concept validation, security hardening, and production scaling. The right partner integrates embedded systems and IoT engineering with cloud-native development, ensuring that firmware, connectivity, and applications behave as one cohesive system.
For your team, this means fewer integration surprises, predictable timelines, and a product that is ready not only to launch, but to operate reliably at scale. The distinction between a vendor that delivers code and a partner that owns the outcome is the difference between a stalled MVP and a product your customers can depend on.
A genuine end-to-end IoT partner is accountable from the first architecture sketch through to production operations — including firmware versioning, cloud observability, OTA pipelines, and documentation that prevents vendor lock-in. Anything less is partial delivery.
What is the typical architecture of an IoT solution?
A typical IoT architecture is built from four interlocking layers: the device layer, the connectivity layer, the cloud and data layer, and the application layer. Each layer carries distinct responsibilities, and the choices you make in one directly impact the others. Power constraints, latency requirements, expected data volumes, and regulatory obligations should drive every architectural decision from day one.
Physical sensors, microcontrollers, and embedded code. Low-power design, robust sensor integration, and on-device preprocessing determine field reliability more than any other factor.
Moves data between device and cloud. Protocol selection (MQTT, CoAP, AMQP) must balance efficiency, reliability, and quality-of-service controls for your specific hardware constraints.
Ingestion, streaming pipelines, time-series storage, role-based dashboards, and APIs. Designing for elasticity from the start avoids expensive rewrites as your fleet grows.
Device and Firmware layer
This is where physical sensors, microcontrollers, and embedded code live. Low-power design, robust sensor integration, and on-device data preprocessing are essential for battery-operated or remote deployments. Firmware quality determines field reliability more than any other factor — a subtle memory leak or a race condition that appears once every ten thousand boot cycles is far harder to diagnose in the field than in a lab environment.
Connectivity layer
This layer moves data between the device and the cloud. Lightweight publish/subscribe protocols such as MQTT — formalized as an international standard in ISO/IEC 20922:2016 — are widely used for constrained devices because they balance efficiency, reliability, and quality-of-service controls. The connectivity choice also determines roaming costs, coverage geography, and the operational model for SIM management or network provisioning at scale.
IoT solutions vs. IoT development services: What is the difference?
“IoT solutions” usually refer to pre-packaged platforms or white-label products. They offer fast time-to-value but tightly constrain customization, branding, and deep integration. IoT development services, by contrast, are bespoke engineering partnerships that build a system tailored to your hardware, your data, your security model, and your business logic.
When your product needs to be a competitive differentiator — not a commodity — custom development is the path that protects your IP and your roadmap. Pre-packaged platforms can accelerate early experiments, but they rarely survive contact with the nuances of a real production environment: proprietary sensor protocols, non-standard ERP integrations, and regulatory requirements that no white-label product anticipated when it was designed.
If you are validating a business hypothesis — not a technical one — a managed platform can compress your time-to-first-data. The key is designing your data model and device interface cleanly so a migration to custom infrastructure is possible without rewriting everything.
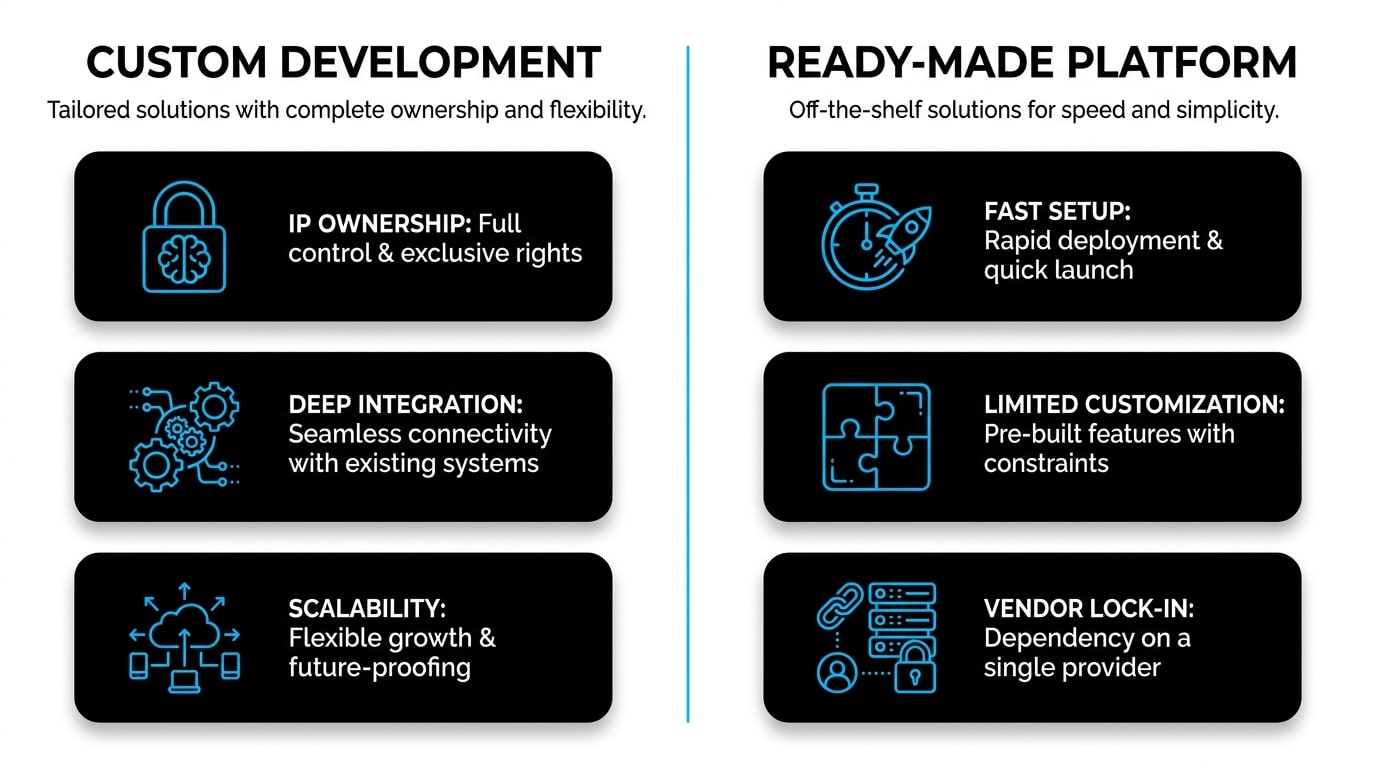
When should you choose custom development over a ready-made platform?

Custom development becomes the right call when your product depends on unique hardware, proprietary security logic, complex regulatory requirements, or non-standard integrations with ERP, CRM, or SCADA systems. It is also the smarter choice when long-term vendor lock-in would compromise your margins or your ability to evolve.
Owning the architecture means owning the future of the product — including the freedom to optimize cost, performance, and user experience as your business scales. Companies that discover this truth after three years on a rigid platform typically face a painful and expensive migration at the worst possible moment: when the business is growing fastest.
- Unique or proprietary hardware requirements
- Strict security or compliance obligations
- Non-standard ERP, CRM, or SCADA integrations
- Long-term IP ownership as a strategic priority
- High data volumes that make per-message pricing prohibitive
- Rapid hypothesis validation with minimal investment
- Standard sensor types with common connectivity needs
- Limited customization requirements
- Short product lifecycle or internal tooling use case
- No regulatory certification requirements
How do you select the right communication technology?
Choosing between Wi-Fi, BLE, Cellular, and LPWAN is one of the highest-impact decisions in any IoT project. The right choice balances power consumption, range, bandwidth, unit cost, and infrastructure availability. A wrong call here can lock your product into expensive operational costs or limit where it can be deployed — and changing connectivity technology after manufacturing begins is rarely feasible within a reasonable budget.
Key selection criteria
Evaluate battery life expectations, expected payload size and frequency, network coverage in target geographies, latency tolerance, and total cost of ownership over the device’s lifetime. A sensor reporting once an hour has very different needs than a real-time industrial controller. LPWAN technologies such as LoRaWAN or NB-IoT are often the right answer for low-bandwidth, wide-area, battery-operated deployments; cellular (LTE-M) suits applications requiring broader geographic mobility; Wi-Fi remains practical for infrastructure-tethered products with abundant power.
Common pitfalls in connectivity
Frequent mistakes include selecting a protocol without testing in real deployment environments, ignoring future regulatory shifts in cellular bands, and underestimating roaming costs for internationally deployed devices. Validating connectivity assumptions during the PoC stage prevents painful and expensive rework after manufacturing begins. A canary deployment of ten devices across your target geographies before committing to a production run is one of the most cost-effective risk mitigation steps available to your team.
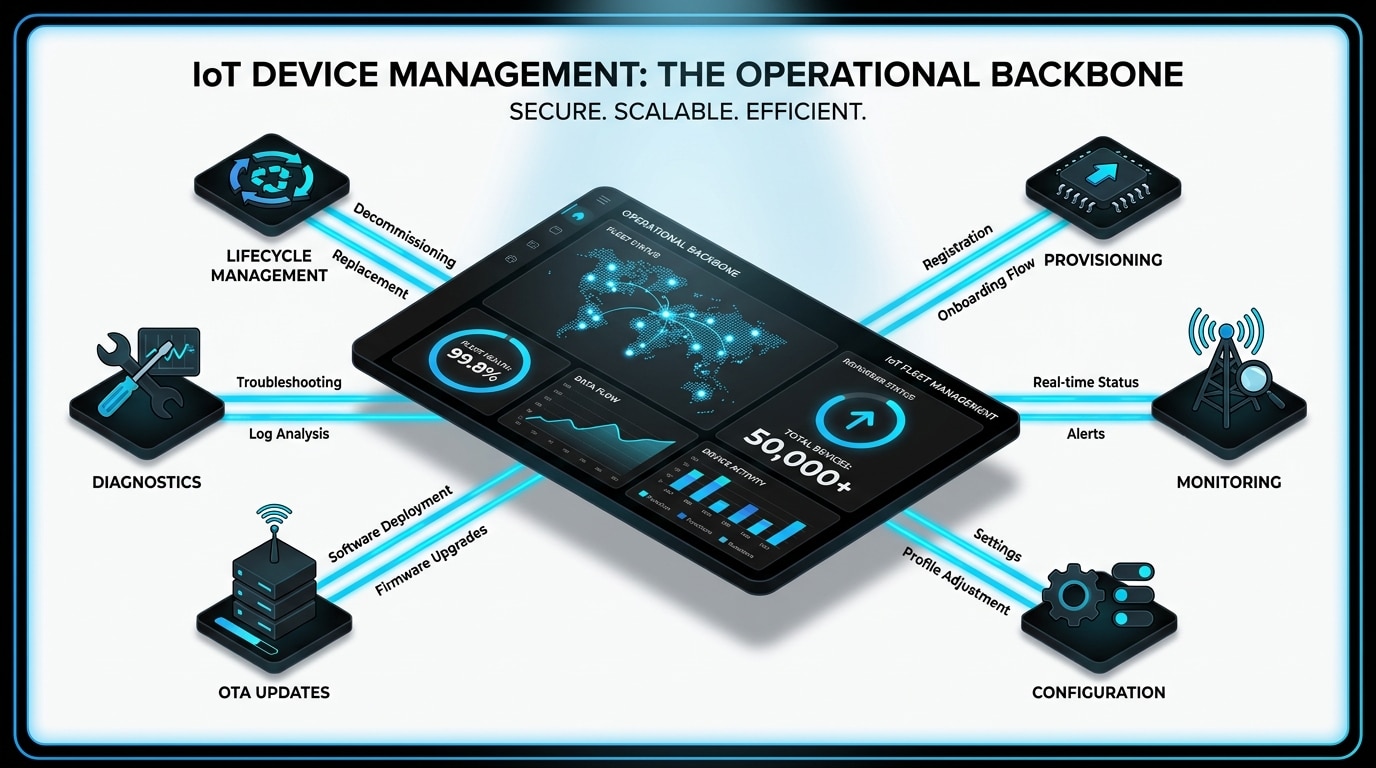
Why is Device Management critical for connected devices?
Device Management is the operational backbone that lets you provision, monitor, configure, and troubleshoot thousands or millions of devices in the field. Without it, every firmware bug, certificate rotation, or configuration change becomes a manual crisis that consumes engineering time and erodes customer trust.
Robust device management enables grouped rollouts, remote diagnostics, lifecycle policies, and graceful retirement of legacy units. In our experience working with scaleups, the absence of mature device management is one of the leading causes of IoT projects stalling between MVP and full production — teams that skipped this investment at the MVP stage consistently pay a disproportionate operational tax as the fleet grows beyond a few hundred units.
Device management is not just an operational concern — it is a security surface. Certificate rotation, remote wipe, and remote deprovisioning capabilities are essential controls that prevent a compromised or end-of-life device from becoming a persistent vulnerability in your network.
How can you implement secure OTA updates?
Secure Over-The-Air updates rely on signed firmware images, version verification, staged rollouts, automatic rollback on failure, and real-time monitoring of update success rates. Canary releases — deploying first to a small subset of devices — catch regressions before they spread to the full fleet.
The NISTIR 8259A baseline for IoT device cybersecurity highlights secure software update mechanisms as a core capability that every connected device should support from day one. A well-designed OTA pipeline transforms firmware updates from a high-risk event into a routine, low-friction operational activity — and gives your team the confidence to ship improvements and security patches continuously rather than deferring them.
How to secure an end-to-end IoT system?
Securing an IoT system requires layered defenses across device, transport, and cloud. The threat model spans device hijacking, telemetry spoofing, data leakage, and supply-chain compromise — each demanding its own controls. Security cannot be retrofitted; it must be designed in from the first architectural decision.
Device identity and secure provisioning
Every device must carry a unique, verifiable identity — typically backed by certificates injected during manufacturing — so it can be authenticated before joining the network. Hardware security modules and secure elements provide tamper-resistant key storage for the most sensitive deployments, ensuring that private keys cannot be extracted even if a device is physically compromised in the field.
Encryption and Key Management
Data must be encrypted both in transit (TLS 1.2 or higher) and at rest, with a clear strategy for key rotation, revocation, and storage in hardware-protected elements where possible. Centralized certificate authority management and automated rotation schedules reduce the operational burden without sacrificing security posture.
Secure development practices
Hardening firmware against tampering, enabling secure boot, signing every release, and following guidance such as the OWASP IoT Project reduces the attack surface and protects users from the most common categories of exploitation. Threat modeling sessions at the architecture phase — not the pre-launch phase — identify the controls worth investing in before they become expensive to implement.
Handling scaling: Moving from 10 to 10,000+ devices
Scaling an IoT system is not a linear exercise. Going from a pilot of ten devices to a fleet of tens of thousands forces a redesign of ingestion, queuing, partitioning, rate limiting, and storage if those concerns were not addressed from the start. Concurrent connections, burst events, and peak data ingestion can degrade systems that worked perfectly in a lab environment within hours of a production rollout.
Auto-scaling cloud architectures, streaming-first pipelines (such as Apache Kafka or cloud-native equivalents), and built-in observability are the foundations that let your platform absorb growth without runaway costs or service outages. Equally important is designing your device-side reconnection and backoff logic so that a cloud restart does not trigger a thundering-herd reconnect storm from the entire fleet simultaneously.
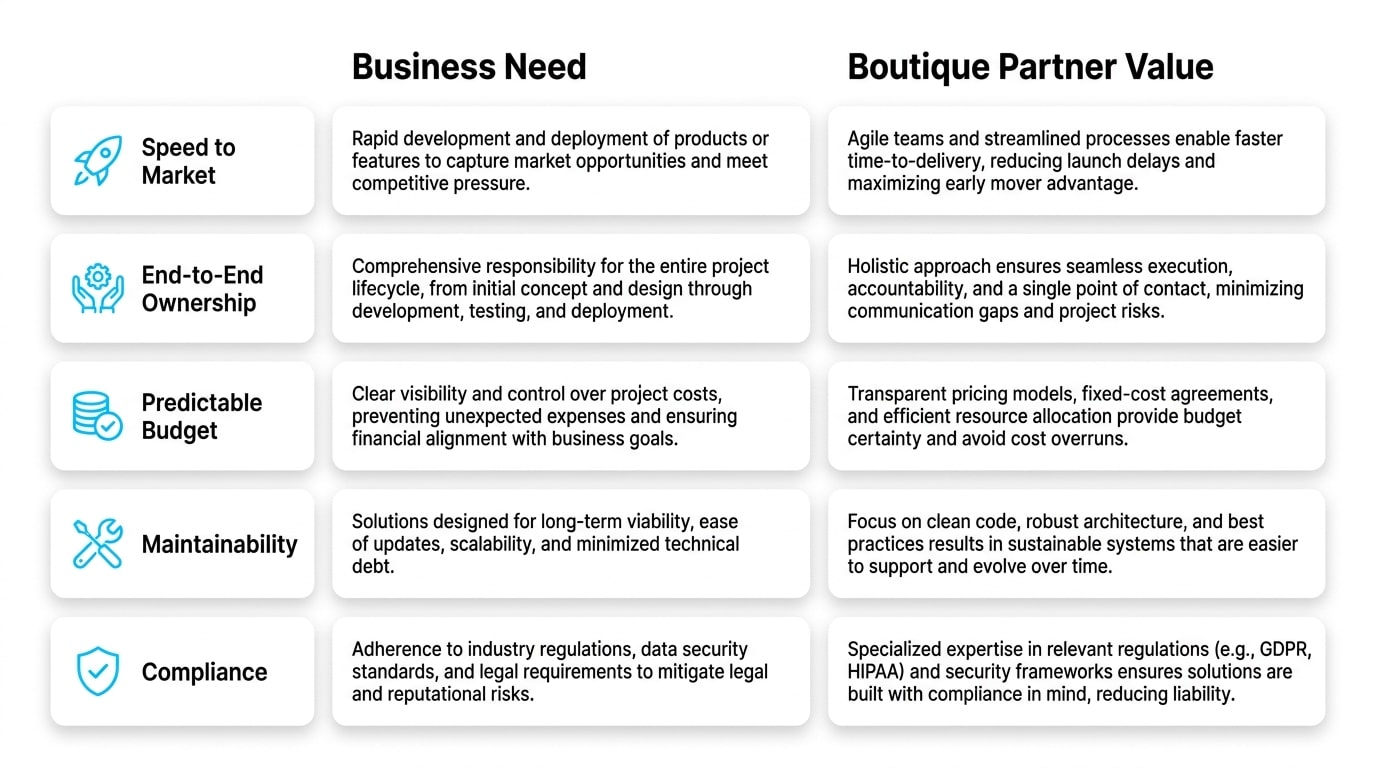
Comparison: business need vs. how a boutique tech partner helps
| Business need | How a boutique partnership delivers in practice |
|---|---|
| Speed to market for a new connected product | An embedded, senior team aligned with your roadmap, working from Discovery through MVP without handoffs or context loss |
| End-to-end ownership of firmware, cloud, and apps | Full-stack IoT engineering under one accountable team, reducing integration friction and eliminating finger-pointing between siloed vendors |
| Predictable budget and scope | Phased delivery with clear milestones, deliverables, and exit criteria at each stage so your team always knows what it is paying for |
| Long-term maintainability | Documented architecture, API specs, and secure deployment guides that prevent vendor lock-in and enable smooth knowledge transfer |
| Compliance and security readiness | Security-by-design practices aligned with recognized baselines and regulatory expectations, built in from day one — not bolted on at the end |
Transforming IoT data into actionable business insights
Raw telemetry has limited value — decisions require context. Effective IoT systems define KPIs early, build clean data models, and surface insights through role-based dashboards and intelligent alerting. Predictive maintenance, anomaly detection, fleet availability metrics, and per-customer usage analytics turn data into measurable operational efficiency.
The goal is not to display every datapoint, but to deliver the right signal to the right stakeholder at the right time. A field service manager needs device health trends and anomaly alerts; an executive needs fleet uptime and revenue-impact metrics; a developer needs raw event logs and error traces. Designing your data model to serve multiple consumer personas from a single source of truth — rather than building parallel reporting stacks — is one of the highest-leverage architectural decisions your team can make.
What is the recommended workflow for a professional IoT project?
A disciplined workflow de-risks complex projects by validating assumptions before scaling investment. Each phase has a defined purpose, deliverables, and success criteria — so you always know what you are paying for and what you are getting in return. Skipping phases rarely saves time; it almost always converts early-stage uncertainty into late-stage rework.
Discovery and Architecture
Define the business problem, map technical risks, sketch the target architecture, and align on cost and timeline assumptions before writing a single line of production code. This phase produces an architecture decision record, a risk register, and a phased delivery plan your team can hold the partner accountable to.
PoC and MVP through Production rollout
Validate the core technical hypothesis — usually connectivity, power, or a critical algorithm — with the minimum investment required to remove the biggest risk. Then build a focused MVP, shifting progressively toward quality assurance, observability, security hardening, and operational stability for the production launch. Each milestone should have explicit acceptance criteria so progress is measurable, not merely claimed.
How long does an IoT development project take?
Timelines depend on the balance between custom hardware needs, software complexity, integrations, and regulatory scope. A focused PoC can be completed in a matter of weeks; an MVP that includes device management, OTA, and a working cloud backend typically spans several months; production hardening adds further time for load testing, certifications, and staged rollouts.
Honest planning prevents the all-too-common pattern of underestimating production-readiness work and overpromising launch dates. The phases most frequently underestimated are: cloud scalability testing, firmware edge-case hardening, security review, and regulatory certification processes — each of which can add weeks or months if not accounted for in the original plan.
Build your project plan backwards from the production launch date, then stress-test every assumption about what “production-ready” means for your specific regulatory context and deployment environment. Surprises discovered during this exercise are far cheaper to resolve in the planning phase than mid-project.
What factors influence the cost of IoT development services?
Cost is shaped by the depth of firmware customization, the number and complexity of integrations, security and compliance requirements, expected data volumes, and ongoing operational support. Building a robust OTA pipeline, designing a scalable data backbone, and certifying a device for specific markets are all line items that should be planned — not discovered mid-project.
Transparent estimation and phased commitments let your team manage budget and risk together rather than absorbing cost surprises in isolation. A partner that provides detailed cost breakdowns by phase — and updates them as scope becomes clearer — is demonstrating the kind of operational discipline you want embedded in your product organization for the long term.
Essential deliverables to request from your engineering partner
Strong deliverables protect your business from key-person risk and vendor lock-in. Request architecture documents, API specifications, data models, hardware schematics where relevant, test plans, security policies, OTA strategy, operational runbooks, and clear ownership of source code and firmware rights at every milestone.
These artifacts make handovers, audits, and future evolution far less painful — and signal that your partner is operating as a true extension of your team rather than a black-box vendor. A partner who is reluctant to produce comprehensive documentation is, in effect, retaining leverage over your product’s future. That is not a partnership; it is dependency by design.
Architecture decision records, API contracts, data schemas, firmware build reproducibility instructions, security threat model, OTA rollout runbook, and full source code ownership with no encumbered licenses. These are baseline expectations, not premium add-ons.
Common mistakes in IoT projects and how to prevent them
| Common mistake | Impact | How to prevent it |
|---|---|---|
| Choosing connectivity without field testing | Costly hardware redesign post-pilot | Validate connectivity in real deployment environments during the PoC phase |
| Skipping device management until production | Inability to operate the fleet at scale without manual intervention | Design provisioning and remote management capabilities from day one |
| Treating security as a final-stage task | Late-stage rework or breaches in the field | Apply security-by-design across all architectural layers from the start |
| Building firmware and cloud in silos | Integration bugs, slow debugging, and blurred accountability | Use a unified, full-stack IoT team under a single delivery accountable |
| Underestimating data scale | Cloud cost explosions and service timeouts at fleet growth points | Plan ingestion architecture, partitioning, and autoscaling from the design phase |
Why hire a full-stack IoT development team?
When firmware, cloud, and application teams operate in silos, integration bugs multiply, debugging slows down, and accountability becomes blurred. Each team blames the adjacent layer, timelines extend, and the product organization loses confidence in its ability to ship. A unified, full-stack IoT team designs the system as a coherent whole: device behavior, network protocols, cloud services, and user experience are aligned from the first architecture session.
The result is faster delivery, cleaner architecture, and a single point of accountability when something needs to be improved or fixed in the field. Shared context across firmware and cloud engineers also dramatically accelerates root-cause analysis when issues arise in production — the person who wrote the firmware protocol handler and the person who wrote the ingestion pipeline are in the same standup, not separated by a ticket queue and a timezone.
Are IoT development services right for your business?
Startups typically need speed to market, lean product definition, and the flexibility to pivot based on early customer feedback. Enterprises require deep system integration, high availability, governance, and compliance with internal and external standards. Both profiles benefit from a boutique tech partnership that becomes an extension of the in-house team — building tomorrow’s connected products together, with the discipline of a senior engineering organization and the flexibility of a partner who adapts to your context.
The key question is not whether your team is technical enough to build it internally — it is whether investing in that capability internally is the best use of your capital and runway at this stage of growth. For most scaleups, the answer is a phased one: start small with an embedded partner, grow the internal team where it creates lasting strategic value, and retain the partnership for depth and continuity where it does.
Frequently asked questions
Do we need to develop both firmware and cloud, or can we start with one?
You can absolutely start small — often with a focused PoC on either the device or the cloud side — but a production-ready IoT product ultimately requires both layers to be designed together. Starting with one layer in isolation is fine for hypothesis validation, but the interface contract between firmware and cloud should be agreed on early to avoid costly integration debt when the two sides eventually meet.
Should we choose Edge computing or a Cloud-only architecture?
Edge processing makes sense when latency, bandwidth, or offline operation are critical — for example, a manufacturing quality-control system that cannot tolerate a 200ms round-trip to the cloud. Cloud-only is simpler when devices have reliable connectivity and data volumes are manageable. Many production systems benefit from a hybrid approach: light preprocessing and anomaly filtering at the edge, with full telemetry forwarded to the cloud for long-term analytics and model retraining.
How do we keep our IP protected when working with an external IoT partner?
Make sure your contract grants you full ownership of source code, firmware, schematics, and documentation from the first commit — not just at project completion. Verify that the partner delivers comprehensive technical artifacts at every milestone, and that no third-party libraries with restrictive licenses are embedded in your firmware or cloud code without explicit disclosure and approval.
Can we start with a small pilot and scale later without rewriting everything?
Yes — if the architecture is designed for scale from day one. The key is making early choices in connectivity, data modeling, device management, and message queue design that will not become bottlenecks when the fleet grows by an order of magnitude. A well-structured pilot with a scalable architecture is far less expensive than a rewrite forced by architectural shortcuts taken under time pressure.
What kind of ongoing support do IoT systems require after launch?
Connected products need continuous monitoring, security patching, OTA updates, infrastructure cost management, and feature evolution. Plan for an operational partnership, not just a one-time build. The operational phase is also where the quality of your architecture documentation and runbooks pays dividends — well-documented systems are far less expensive to support over time than undocumented ones.
How do we measure the success of an IoT development project?
Define KPIs early and agree on them with your engineering partner before development begins: device uptime percentage, data accuracy rates, mean time to deploy OTA updates, cloud infrastructure cost per active device, and business outcomes such as reduced field service calls, new revenue streams enabled, or measurable reduction in equipment downtime. KPIs defined after launch are difficult to baseline and easy to dispute.
What certifications might our connected product require before launch?
Requirements vary by product category, target geography, and deployment environment. Common certifications include radio frequency approvals (FCC in the US, CE in Europe), electrical safety standards, and industry-specific compliance such as IEC 62443 for industrial automation or MDR for medical devices. Certification timelines should be built into the project plan from the Discovery phase — retrofitting a design to meet certification requirements is one of the most avoidable and expensive delays in IoT product development.
How should we approach multi-tenant IoT deployments where data isolation is critical?
Multi-tenancy in IoT requires careful design at the data model, API, and device provisioning layers. Each tenant’s device fleet, telemetry, and configuration should be logically isolated — ideally enforced at the data store and API gateway level rather than relying solely on application-layer checks. Design your tenant onboarding and device provisioning workflows to support this isolation model from the first device enrolled, not as a retrofit when a second enterprise customer arrives.


