Secure Development Services: Building Software That’s Secure by Design
Embed security into every stage of your SDLC — ship faster, reduce risk, and earn lasting customer trust.
- Secure development services embed security expertise inside your SDLC, not as a final gate but as a continuous engineering discipline throughout every sprint.
- Shifting security left — to the design and coding stage — dramatically reduces remediation cost, rework time, and late-cycle release blockers.
- SAST, DAST, and SCA cover complementary attack surfaces; professional triage transforms raw scan output into prioritized, actionable developer work.
- Effective measurement focuses on MTTR, defect leakage, and secure coding adoption — not vanity metrics like scan count or tickets opened.
- A right-sized pilot delivers fast tactical wins; a follow-on retainer turns those wins into a sustainable, compounding security posture.
- Compliance evidence — policies, threat models, pipeline logs — is generated as a natural output of daily engineering work, not assembled before each audit.
Table of Contents
- What are secure development services and what do they include?
- Why do organizations choose a security-first approach?
- Secure development services vs. general application security
- What is secure coding and how does it differ from clean code?
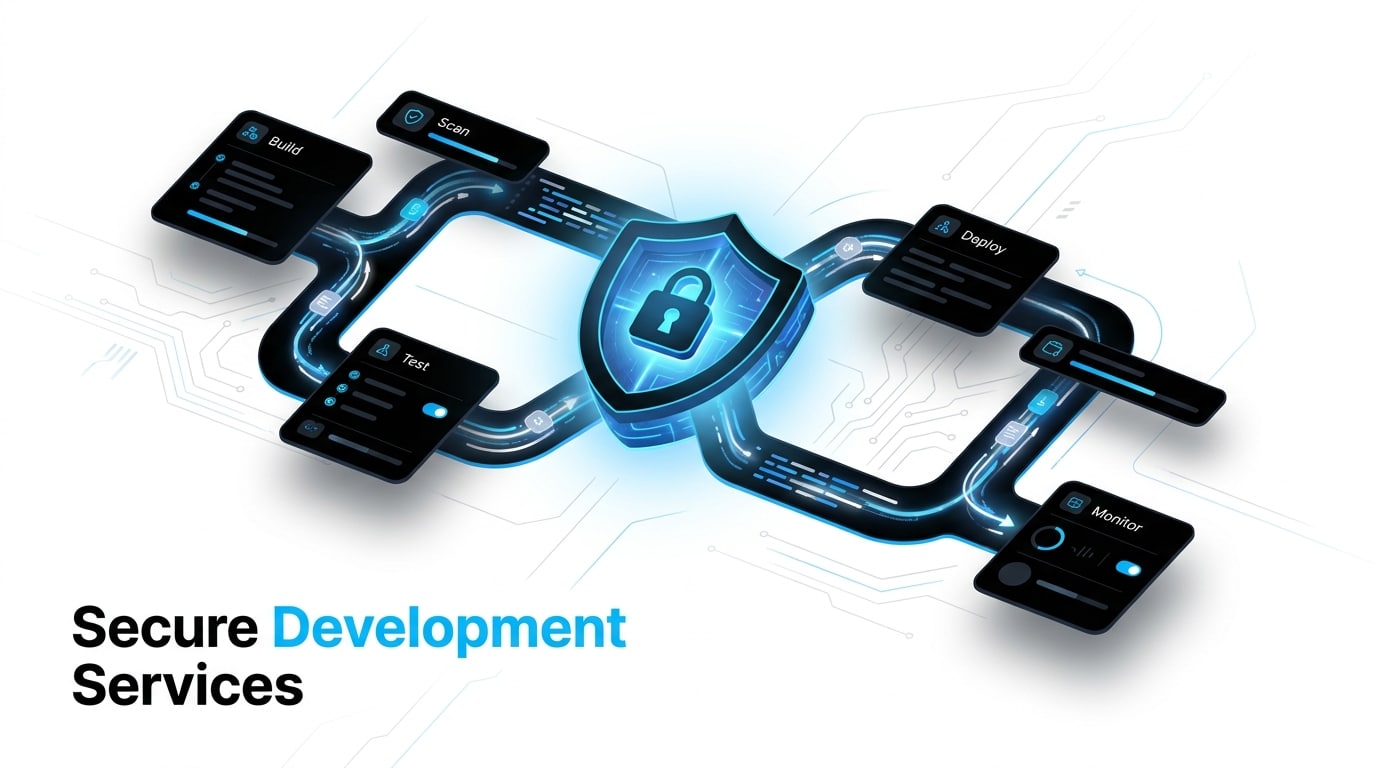
- How is the workflow for secure development services structured?
- What deliverables should you expect?
- How can threat modeling be implemented in Agile?
- Why are SAST, DAST, and SCA essential components?
- How do secure development services protect the CI/CD pipeline?
- What is a Secure SDLC and how is it constructed?
- Mapping business needs to what you actually get
- Point-in-time consulting vs. retainer-based model
- What is the typical timeline for seeing ROI?
- What factors influence the cost?
- How should security success be measured?
- Can these services assist with compliance requirements?
- How are OWASP Top 10 risks mitigated?
- Common mistakes when adopting secure development
- Frequently asked questions
For today’s fast-moving startups and scaleups, shipping software quickly is no longer enough. Every release carries a security footprint, and a single vulnerability that escapes into production can erode user trust, trigger compliance issues, and stall your roadmap for weeks. That’s why secure development services have become a strategic investment rather than an optional add-on — they embed security expertise directly into your engineering workflow so your team can build faster while reducing risk at the same time.
In this guide, you’ll discover how these services work in practice, what to expect from a strong partner, and how to measure real impact across your SDLC. Whether you’re a startup establishing secure foundations or a scaleup hardening a complex product organization, Sentice brings the embedded engineering experience and full-SDLC perspective to help you build tomorrow’s solutions, together.
What are secure development services and what do they include?
Secure development services combine security engineering, process integration, and proven best practices that live inside your software development lifecycle — not next to it. Instead of treating security as a final checkpoint, you get dedicated engineering teams that work alongside your developers to harden the product as it’s built. A typical engagement covers security requirements gathering, threat modeling, secure coding standards, automated pipeline testing, targeted code reviews, and remediation support until issues are fully closed.
The outcome is straightforward: your application security posture improves continuously, and your team gains the patterns and tooling to maintain it independently. For scaleups, this approach means fewer surprises during audits and a more predictable release cadence — without sacrificing engineering velocity.
Hands-on engineering work to harden your codebase, pipelines, and architecture — delivered by senior practitioners embedded in your team’s daily workflow.
Security practices woven into sprints, PR reviews, and planning rituals — so your team builds securely by default without adopting a parallel process.
Ongoing triage, tuning, and standards updates that keep your defenses aligned with evolving threats and growing product complexity over time.
Why do organizations choose a security-first approach instead of fixing flaws at the end?
Fixing vulnerabilities late in the cycle is expensive, slow, and risky. Patching a flaw discovered in production can cost dramatically more than catching it during design or code review, and the delay often blocks new feature releases. A security-first approach reduces this “security debt” by addressing risks at the architecture and coding stage, where changes are cheap and contextual.
Initiatives like the CISA Secure by Design Pledge formalize this shift, encouraging vendors to treat security as a foundational business requirement rather than a compliance afterthought. By shifting left, your team gains predictability, faster audits, and stronger trust with customers — three outcomes every scaling product company needs.
Research consistently shows that vulnerabilities discovered in production cost significantly more to remediate than those caught during design or code review — both in direct engineering hours and in the downstream impact on release schedules, customer trust, and compliance standing. Shifting left is not just a security principle; it is a business efficiency decision.
Is there a real distinction between secure development services and general application security?
Yes, and understanding the difference matters when scoping a partnership. Application security is the umbrella discipline covering strategy, governance, testing, monitoring, and incident response. Secure development services, by contrast, focus specifically on the hands-on engineering phase — where code is written, reviewed, and shipped.
A capable partner emphasizes continuous education for your developers, operationalizes secure coding patterns inside your repositories, and builds guardrails into your pipelines. The goal is not to produce another report, but to embed security as a daily engineering habit. Together, the two layers form a complete picture, with secure development serving as the practical engine that makes broader application security strategies actually work.
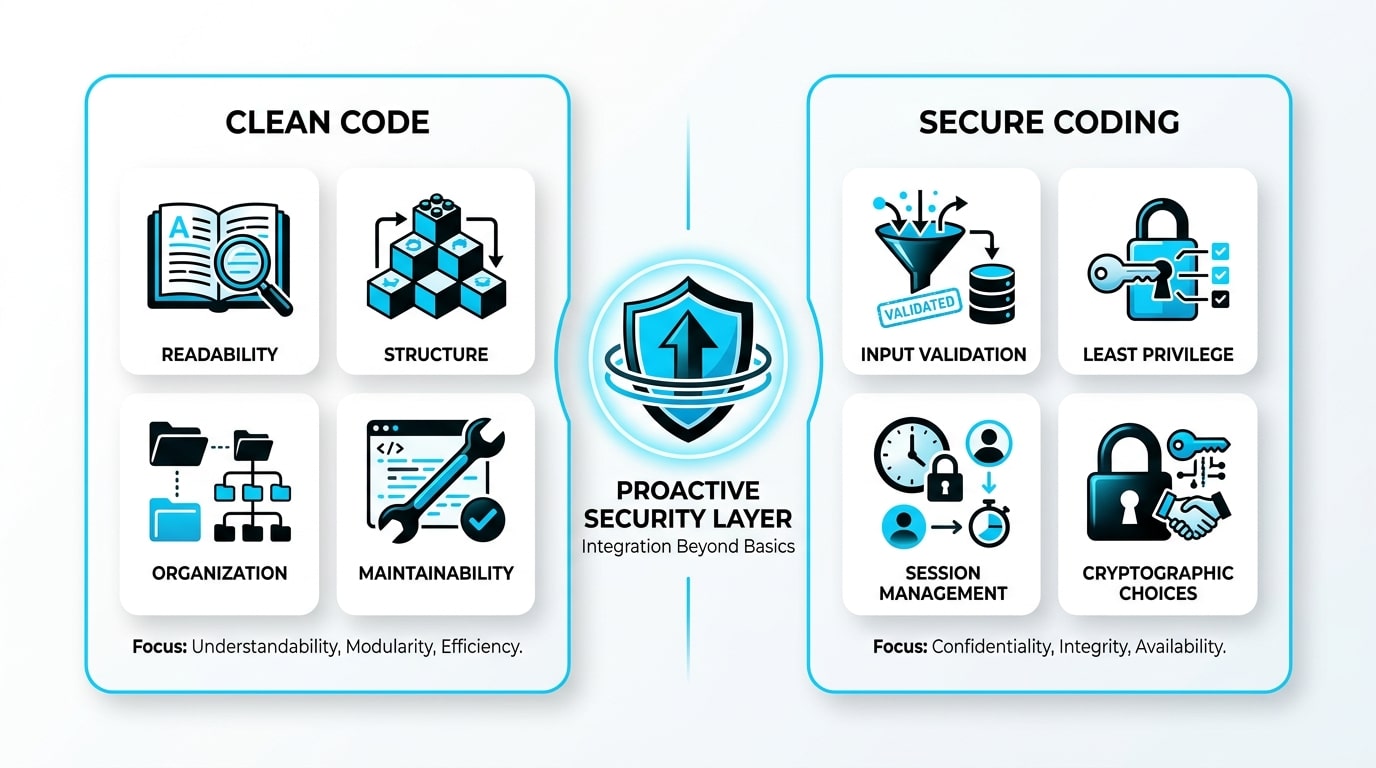
What is secure coding and how does it differ from standard clean code?
Clean code focuses on readability, maintainability, and structure. Secure coding goes further: it’s a proactive discipline aimed at preventing entire classes of vulnerabilities such as injection, broken authorization, XSS, and insecure deserialization. In practice, that means context-sensitive input validation, applying the principle of least privilege, secure session management, careful cryptographic choices, and never embedding secrets in source files.
The OWASP Developer Guide remains a foundational reference here, offering reusable patterns your team can adopt without reinventing the wheel. The key insight: clean code can still be insecure, and secure code is rarely accidental — it requires intent, training, and reinforcement.
- Readability and naming conventions
- Logical structure and modularity
- Test coverage and maintainability
- Consistent formatting and documentation
- Refactoring and technical debt reduction
- Input validation and output encoding
- Principle of least privilege applied
- Secrets management and cryptography
- Secure session and auth patterns
- Prevention of injection and XSS classes
How is the workflow for secure development services typically structured?
A mature workflow starts with diagnosis, moves into integration, and matures into a measurable routine. The exact steps vary by organization, but the structure remains consistent across engagements that deliver real value rather than checkbox compliance.
Initial baseline assessment and metric definition
The engagement begins by mapping your current state: existing controls, known risks, repository structure, and pipeline maturity. Baseline metrics — such as open critical findings or average remediation time — are defined upfront so progress can be tracked objectively rather than anecdotally. This phase typically surfaces quick wins alongside the deeper systemic gaps that a sustained engagement will address.
Integrating security into sprints without disrupting velocity
Security tasks are introduced as sprint-friendly work items: small, scoped, and tied to specific features. Rather than imposing a parallel process, the partner aligns with your team’s existing rituals — standups, planning, retros — so security becomes part of how you already build. Over time, developers internalize the patterns and apply them without additional friction.
Maintaining a continuous cycle of triage and prevention
Once integrated, the focus shifts to sustained operation: triaging new findings, tuning automation to reduce false positives, and updating standards as threats evolve. This is where long-term partnerships consistently outperform one-time audits — the compounding effect of each sprint reinforcing the previous one drives measurable, lasting improvement.
The most effective engagements begin with a tightly scoped pilot — one or two repositories, one product team — that produces concrete wins within the first few weeks. Those wins build internal alignment and justify expanding the scope across your broader engineering organization.
What deliverables should you expect from a secure development service?
Strong partners produce deliverables that drive engineering action, not glossy decks. You should expect a prioritized backlog mapped to risk, secure coding guidelines tailored to your stack, threat models for critical features, PR-level checklists, CI policy definitions, and security-focused acceptance criteria templates.
Actionable deliverables for developers
Tickets with reproduction steps, suggested fixes, and code references. PR guidance and reusable security patterns. Lightweight playbooks the team can apply during reviews without slowing merges. The emphasis is on tools and references that become part of daily practice rather than documents that live in a shared drive untouched.
Evidence-based deliverables for management
Dashboards tracking MTTR, defect leakage, and adoption rates. Documented policies, threat models, and audit-ready evidence that demonstrates a working process — not just intentions. These outputs directly support enterprise customer reviews, SOC 2 audits, and board-level reporting, turning security from a cost line into a credibility asset.
How can threat modeling be implemented in Agile without causing bottlenecks?
Threat modeling becomes a bottleneck only when it’s treated as a separate ceremony requiring full-team assembly and multi-hour workshops. The lightweight approach focuses on critical features as they enter the design phase: the team identifies data flows, trust boundaries, key assets, and the most plausible attack paths. The output isn’t a 40-page document — it’s a handful of concrete security tasks added directly to the sprint backlog.
By using consistent templates and limiting scope to high-impact components, application security work fits naturally into existing planning cycles. Teams that adopt this approach find that developers start applying threat-modeling questions instinctively during feature design — exactly the cultural shift that mature secure development services aim to create over a sustained engagement.
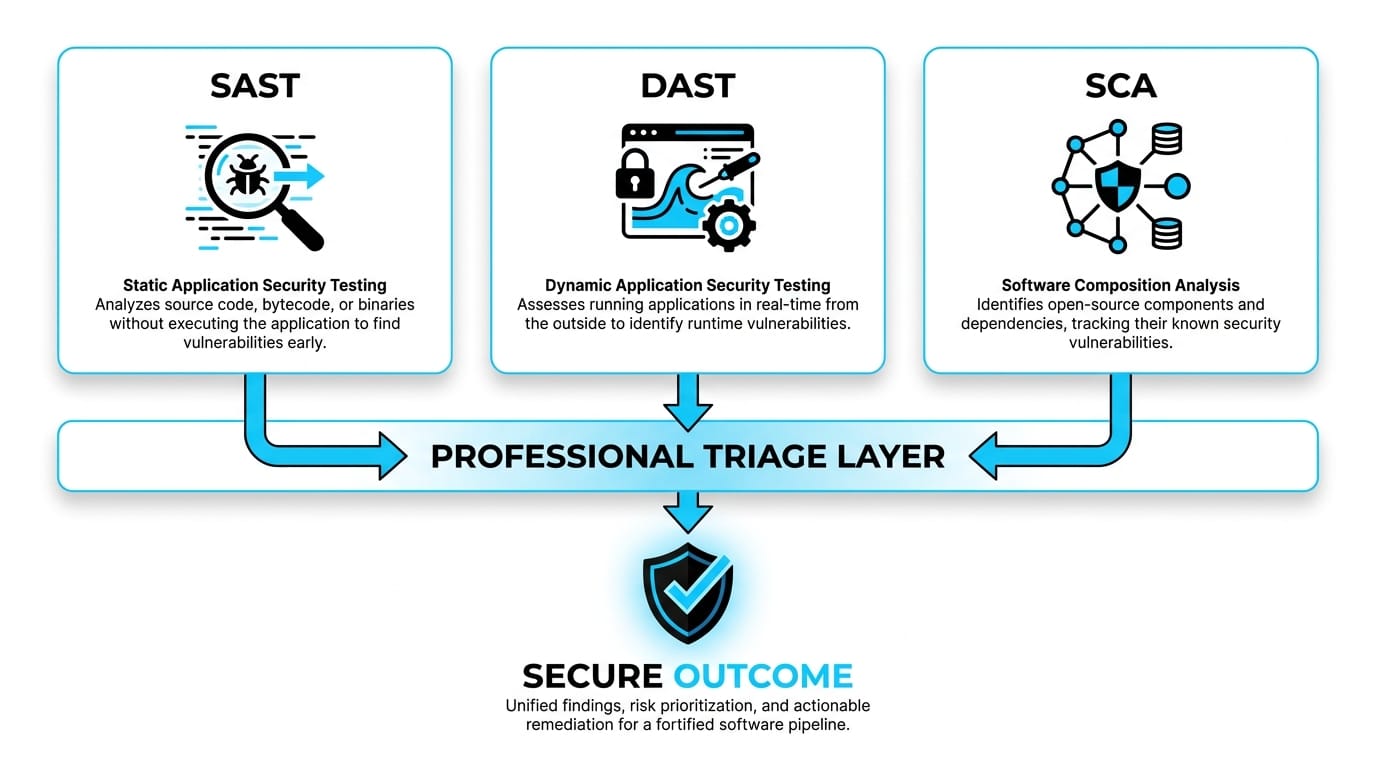
Why are SAST, DAST, and SCA essential components of these services?
These three testing categories cover complementary attack surfaces. SAST analyzes source code statically to catch insecure patterns early, before the application ever runs. DAST exercises the running application to surface behavioral and runtime vulnerabilities that static analysis cannot detect. SCA inspects third-party dependencies and open-source components — increasingly the largest source of risk in modern applications given the prevalence of supply-chain attacks.
Tools alone, however, are not the differentiator. The real value comes from professional triage: filtering noise, prioritizing exploitable findings, defining clear policies, and integrating results into developer workflows. Without that discipline, scanners produce alert fatigue and ignored backlogs. With it, they become a reliable early-warning system that catches issues before they reach customers.
Static Application Security Testing analyzes source code and binaries without executing the application — ideal for catching insecure patterns at the coding stage during CI.
Dynamic Application Security Testing probes the running application from the outside, surfacing runtime and behavioral vulnerabilities that static analysis cannot reach.
Software Composition Analysis inventories third-party and open-source dependencies, flagging known vulnerabilities and license risks in your supply chain.
How do secure development services protect the CI/CD pipeline?
Modern pipelines are both an accelerator and a target. Securing them means installing automated guardrails that catch critical issues before merge or deploy, while keeping developer experience smooth enough that teams don’t route around the controls.
Block versus Warn policies
Critical findings should block the build; lower-severity issues warn and create tracked tickets. The balance prevents pipeline paralysis while ensuring real risks never slip through silently. Calibrating this threshold correctly — and revisiting it as your codebase matures — is one of the most valuable contributions a seasoned partner brings.
Managing exceptions and temporary bypasses responsibly
Exceptions are inevitable in any active product organization. What matters is governance: every bypass has an owner, a justification, an expiration date, and a follow-up ticket. This discipline keeps short-term flexibility from compounding into long-term risk that surfaces at the worst possible time — during an audit or customer review.
Secrets, permissions, and artifact signing
Secrets management, scoped pipeline permissions, container image scanning, and signed artifacts together form the operational backbone of a trustworthy delivery pipeline. These controls are especially important as pipelines grow in complexity and more contributors interact with them across distributed teams.
Pipeline misconfiguration and exposed secrets in CI/CD environments have become a primary attack vector in high-profile supply-chain breaches. Scoped permissions and secrets rotation are among the highest-ROI controls a product team can implement, often in a single sprint with the right guidance.
What is a Secure SDLC and how is it constructed programmatically?
A Secure SDLC is a framework of measurable, auditable practices applied across every stage of software production — from requirements through deployment and incident response. Rather than rebuilding from scratch, most teams adopt an established model and tailor it to their context and risk profile.
The NIST SP 800-218 Secure Software Development Framework (SSDF) offers a widely respected blueprint covering governance, secure design, secure implementation, verification, and release and response. The practical path is to define a minimum required set of controls per stage — design reviews, testing gates, release criteria — and expand maturity as your organization grows. Done right, your Secure SDLC becomes a competitive advantage that accelerates enterprise sales cycles, not an overhead that slows your team down.
Mapping business needs to what you actually get
One challenge leaders face is connecting abstract security capabilities to concrete business outcomes. The table below illustrates how a partnership-driven model translates real needs into tangible support — without promising silver bullets.
| Business Need | How a Secure Development Partner Helps in Practice |
|---|---|
| Ship features faster without security regressions | Embedded engineers integrate security into sprints and PR reviews, removing late-stage rework and release blockers |
| Pass enterprise customer security reviews | Generate audit-ready evidence, threat models, and policy documentation alongside the build as a natural output |
| Reduce open critical vulnerabilities | Prioritized remediation backlog with measurable MTTR improvements tracked sprint over sprint |
| Scale a small security function | Flexible engagement model that augments in-house capacity without long hiring cycles or onboarding overhead |
| Strengthen secure coding culture | Reusable patterns, hands-on enablement, and PR-level guidance tailored to your specific stack and team |
Is point-in-time consulting better than a retainer-based model?
For most organizations, the answer is a hybrid. A short pilot proves value quickly, identifies high-impact gaps, and builds internal alignment for deeper investment. A retainer that follows turns those wins into a sustainable routine — preventing regressions, supporting new features, and adapting to evolving threats as your product grows.
Point-in-time engagements work well for a single product launch or a focused remediation push, but they rarely create lasting change in how your team builds software. A retainer makes sense when releases are frequent, multiple teams ship in parallel, or compliance obligations require continuous evidence. The decision should match your risk profile and release cadence, not a generic vendor recommendation.
What is the typical timeline for seeing ROI from these services?
Realistic expectations matter. Tactical wins — improved triage, faster remediation of critical findings, cleaner PRs — typically appear within the first few weeks of an engagement. Systemic change, where new vulnerabilities decrease, secure coding patterns are adopted broadly, and audit preparation becomes routine, usually emerges across two to three months.
Timelines depend on team size, release frequency, and accumulated technical debt. Early metrics worth tracking include time-to-remediate critical issues, the rate of new high-severity findings per sprint, and PR review quality over time. Organizations that commit to the process consistently see compounding returns: each sprint reinforces the previous one, and the security posture strengthens without dragging down velocity. DORA metrics — deployment frequency, change failure rate, and mean time to restore — often improve alongside security outcomes when the two disciplines are integrated rather than siloed.
What factors influence the cost of secure development services?
Cost depends on scope, depth, and starting maturity. Key drivers include the number of repositories and products in scope, the size and structure of your engineering teams, regulatory requirements, and the depth of hands-on involvement — advisory versus embedded engineering. The volume of remediation work needed upfront and the complexity of your CI/CD pipeline integration also influence pricing meaningfully.
Most engagements are structured into tiers: a focused pilot, an ongoing retainer, or a full-scale rollout across the organization. This structure lets you match investment to current priorities and demonstrate internal ROI before committing to broader expansion. The most cost-effective path almost always starts with a tightly scoped pilot — one team, one product area — that produces measurable wins before scaling the partnership.
How should security success be measured beyond vanity metrics?

Counting scans run or tickets opened tells you nothing about risk reduction. Effective measurement focuses on operational outcomes that reflect genuine change in engineering behavior and product posture.
- Mean Time to Remediate (MTTR) for critical vulnerabilities
- Defect leakage — issues reaching production vs. caught earlier
- Recurrence rate of the same vulnerability classes
- False-positive ratio after pipeline tuning
- Secure coding standard adoption rate across teams
- PR review quality scores over time
- Threat models completed per new feature
- Developer enablement session completion rates
Together, these metrics give leadership a clear narrative for board updates and customer security questionnaires — turning security from a cost center into a credibility asset that accelerates enterprise sales and strengthens long-term trust.
Can secure development services assist with compliance and regulatory requirements?
Yes, and this is one of their highest-leverage benefits. Frameworks like SOC 2, ISO 27001, HIPAA, and PCI DSS all require evidence of a secure development process — not just final test results or point-in-time attestations. By generating policies, threat models, code review records, and pipeline logs as a natural output of daily work, these services dramatically reduce audit preparation time and the anxiety that typically accompanies it.
A trusted technical advisor can also help you align controls with multiple frameworks simultaneously, avoiding duplicated effort and conflicting interpretations. For scaleups pursuing enterprise customers, this evidence trail is often the difference between closing a security review in weeks versus months. To learn more about long-term technical partnership models that support compliant growth, explore end-to-end software solutions for startups and scaleups.
How are OWASP Top 10 risks mitigated through professional development services?
The OWASP Top 10:2021 remains the industry consensus on the most critical application risks, covering categories like broken access control, injection, insecure design, and vulnerable and outdated components. Professional secure development services translate these categories into concrete daily practices rather than awareness exercises.
PR review checklists, automated CI gates, secure-by-default framework configurations, and architecture patterns prevent reintroduction of known flaw classes. Broken access control is addressed through centralized authorization layers and consistent test coverage. Injection risks are mitigated via parameterized queries and validation libraries enforced at the platform level. Vulnerable dependencies are surfaced continuously by SCA integrated into your pipeline. The goal is not awareness — it’s prevention engineered into the codebase so the same flaw never reaches production twice.
Common mistakes organizations make when adopting secure development
Several patterns repeatedly undermine otherwise well-intentioned security programs. The first is treating security as a one-time project rather than an ongoing engineering discipline — a single engagement that produces a report and then goes dark. The second is over-investing in tools without investing in triage, tuning, and developer enablement, producing alert fatigue and ignored backlogs instead of risk reduction.
A third mistake is isolating security from product planning, which guarantees friction every time security priorities collide with feature commitments. Finally, many teams skip the baseline measurement phase entirely, making it impossible to demonstrate progress or justify continued investment. Avoiding these traps doesn’t require more budget; it requires aligning security work with how your engineering organization already operates — and choosing a partner who understands that the goal is cultural change, not just compliance output.
Deploying scanners without investing in professional triage is one of the most common and costly mistakes teams make. Untuned scanners generate thousands of findings, most of which are false positives or low-severity noise. Developers learn to ignore the alerts entirely — which means real, exploitable vulnerabilities hide in plain sight. The investment in triage and tuning typically delivers more risk reduction than the scanner itself.
Frequently asked questions
How quickly can a secure development engagement begin delivering value?
Most engagements show tactical results — improved triage, cleaner PRs, faster remediation of critical findings — within the first few weeks. Systemic improvements, where new vulnerability rates decline and secure coding patterns are broadly adopted, typically emerge over two to three months as standards are embedded and pipelines mature.
Do secure development services replace the need for penetration testing?
No. Penetration testing validates your defenses from an attacker’s perspective at a specific point in time, surfacing logical and architectural weaknesses that automated tools miss. Secure development services prevent vulnerabilities from being introduced in the first place. The two disciplines are complementary and work best together as part of a layered security program.
Are these services suitable for early-stage startups?
Yes. Startups often benefit the most from early engagement because building secure foundations avoids costly refactoring and rearchitecting later. A right-sized pilot can deliver high-impact improvements without overwhelming a small team, and the patterns established early scale naturally as the product and engineering organization grow.
What level of access does a secure development partner need to our codebase?
Typically read access to repositories, integration with CI/CD systems, and collaboration access in your issue tracker are sufficient to begin. All access follows least-privilege principles and is governed by formal agreements aligned with your security and data policies. Access scopes are reviewed and adjusted throughout the engagement as needed.
Can secure development services support multiple tech stacks simultaneously?
Yes, when the partner has genuine cross-stack expertise. Standards, threat models, and pipeline guardrails are tailored per stack while sharing common governance and measurement frameworks, so polyglot environments remain manageable and consistent. This is particularly important for product organizations that have grown through acquisition or rapid hiring.
How do these services handle legacy code with significant technical debt?
Through risk-based prioritization rather than wholesale rewrites. The partner focuses remediation effort on the highest-impact areas first — authentication, authorization, data handling, and external interfaces — and incrementally hardens the rest as features are naturally touched during normal product development. This approach delivers measurable risk reduction without stalling the roadmap.
What happens after the engagement ends?
Mature engagements transfer ownership progressively throughout the partnership, not only at the end. Documented standards, trained developers, automated guardrails, and clear operational runbooks remain in place so your team can sustain the practice independently. Many organizations choose to extend the partnership on a lighter retainer to maintain continuity as the product evolves.
How does secure development differ from a traditional security audit?
A traditional security audit produces a point-in-time snapshot of your posture — useful, but unable to prevent the next vulnerability introduced the following sprint. Secure development services are embedded and continuous, changing how code is written, reviewed, and shipped day to day. The result is a living security posture that improves alongside your product rather than one that ages between audit cycles.


